Что такое вирус hydra
Кругозор без горизонтов
Чтобы получить доступ к сервисам проекта, войдите на сайт через аккаунт. Если у вас еще нет аккаунта, его можно создать.

- добавить в избранное
![]()
Для тех, кому за 30
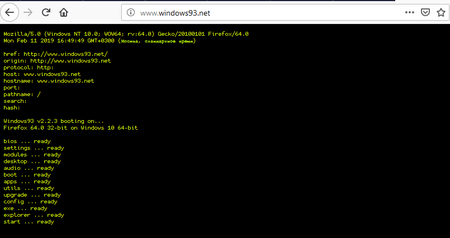
Вирусы есть везде! Даже в Windows 93. Говорите, такой операционной системы не существует, а потому и вирусов для нее нет? Вы в корне не правы.
Многие помнят загрузку в виде потока строк с информацией. (А кто помнит, что первые Windows были не операционной системой, а всего лишь операционной средой и загружались из DOS?)
Строки смутно напоминают флаг (а впрочем, сколько раз Microsoft меняла вид логотипа?).
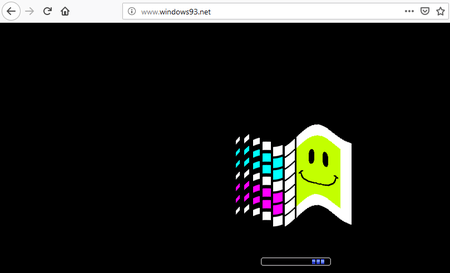
И вот мы в Windows 93!
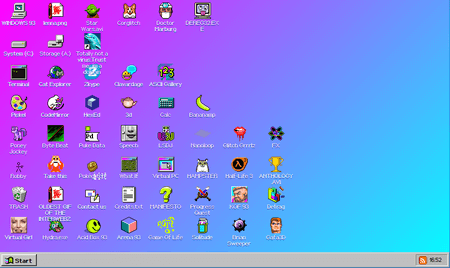
Сначала вирусы. Мы нашли сразу два — и оба нагло расположились на рабочем столе.
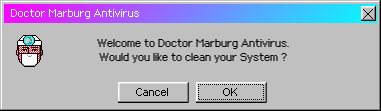
Начнем с Hydra. Смело жмем на ярлык.
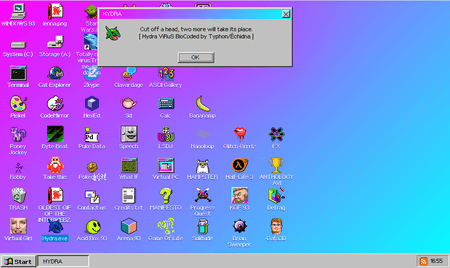
Соглашаемся, нажимаем ОК — и окно начинает двоиться!
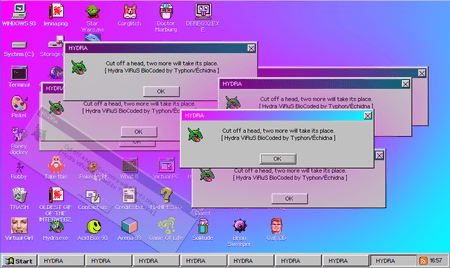
Правда, некоторые окошки выпадают. Может быть, это обещанная встроенная антивирусная защита?
Второй троянец — Dolphin, уверяющий нас, что он совсем не вирус. Честно-честно.

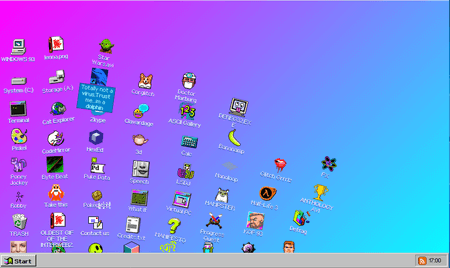
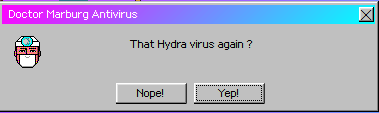
Ой, что это? Всё посыпалось! Но у нас есть антивирус Doctor Marburg! Запускаем.
После перезагрузки внешний вид рабочего стола восстановлен. А вот Hydra этому антивирусу не по зубам.
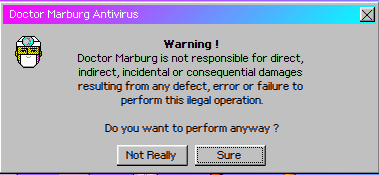
Если что, нас честно предупреждают:
И начинают интересоваться нашей банковской картой.
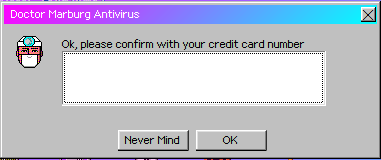
Ладно, нажимаем ОК.
Набор имеющихся в Windows 93 программ может оправдать интерес к этой системе. Но встроенный антивирус не выдерживает никакой критики, и мы рекомендуем его заменить.
Получайте Dr.Web-ки за участие в проекте
Каждая активность = 1 Dr.Web-ка


Sergey
10:08:16 2020-03-21
I23
10:45:33 2019-04-02
I46
09:57:17 2019-04-02
Lenba
09:29:08 2019-04-02
razgen 
23:48:29 2019-04-01
Lia00 
22:43:28 2019-04-01
Шалтай Александр Болтай 
22:39:14 2019-04-01
Шалтай Александр Болтай 
22:31:51 2019-04-01
Любитель пляжного футбола 
22:00:07 2019-04-01
Andromeda
21:30:03 2019-04-01
Альфа
21:21:24 2019-04-01
orw_mikle
21:13:35 2019-04-01
Dvakota
21:05:34 2019-04-01
matt1954
20:17:37 2019-04-01
anatol
20:08:33 2019-04-01
maestro431
19:48:55 2019-04-01
Геральт 
18:34:57 2019-04-01
Татьяна
18:04:49 2019-04-01
Rider
17:54:46 2019-04-01
robot
17:39:30 2019-04-01
Toma
16:07:11 2019-04-01
Masha
14:47:52 2019-04-01
eaglebuk
13:34:08 2019-04-01
Oleg
12:57:53 2019-04-01
Ярослав
12:53:00 2019-04-01
tigra 
12:49:55 2019-04-01
Денисенко Павел Андреевич
12:17:27 2019-04-01
Dmur
12:15:50 2019-04-01
Anton_S
11:43:33 2019-04-01
Неуёмный Обыватель 
11:35:44 2019-04-01
vinnetou
11:11:50 2019-04-01
sanek-xf
10:29:53 2019-04-01
Natalya_2017
10:24:40 2019-04-01
vkor
10:20:30 2019-04-01
EvgenyZ
09:47:07 2019-04-01
marisha-san 
09:22:44 2019-04-01
achemolganskiy
08:19:33 2019-04-01
Пaвeл 
08:14:27 2019-04-01
B0RIS
08:04:32 2019-04-01
dyadya_Sasha 
07:54:40 2019-04-01
Vlad X
07:42:30 2019-04-01
GREEN 
07:32:18 2019-04-01
Alexander 
07:20:35 2019-04-01
Симпатичный прикол. Привет-улыбка из "прекрасного Далёко". И на смартфоне работает. Всё по-взрослому. И кнопка "Start", и выпадающее меню. окна. ярлыки. команды.
P.S. . а вот интересно. появится ли спам-рассылка первоапрельских писем со ссылкой на страничку windows93.net. . :))
Korney
07:05:22 2019-04-01
Любитель пляжного футбола 
07:00:36 2019-04-01
ka_s
06:59:35 2019-04-01 
L1t1um
06:12:00 2019-04-01
Morpheus 
05:51:48 2019-04-01
SGES 
03:44:00 2019-04-01
Hydra ransomware – malware that comes camouflaged as Mozilla Firefox
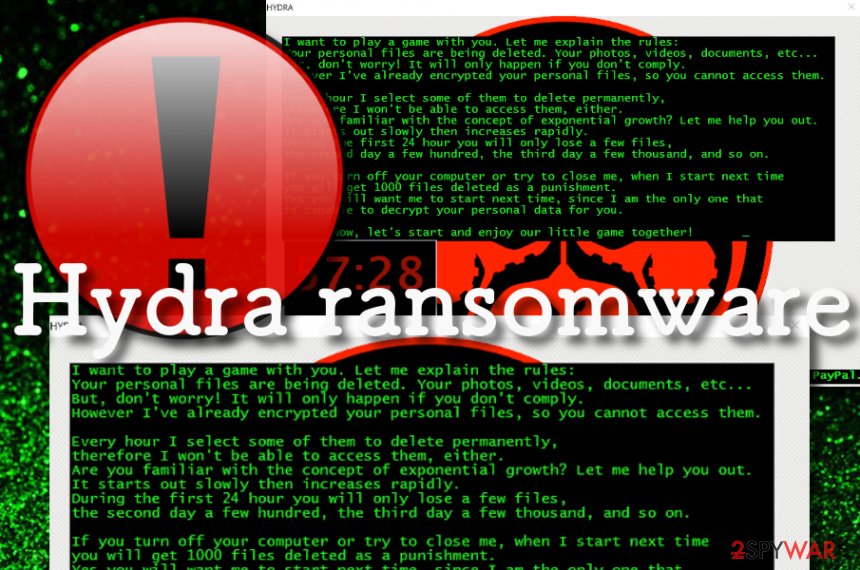
Hydra virus - ransomware that camouflages as the Mozilla Firefox process
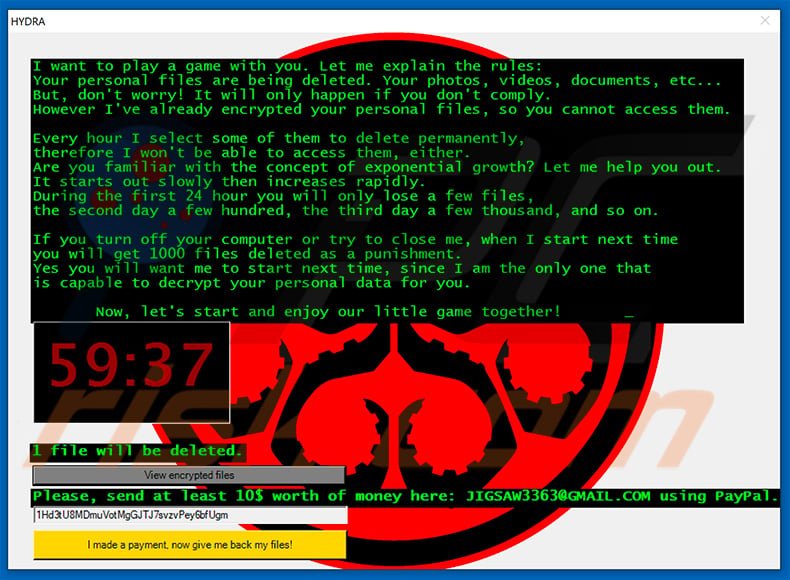
Hydra ransomware is a cyber infection that threatens victims to delete their files if they do not meet the ransom demands. The malware attack starts with a secret infiltration process through an infected email spam attachment or a cracked piece of software that the user has downloaded from a torrenting network. Afterward, Hydra virus runs the encryption module by using a cipher such as AES or RSA [1] and targets all the data that is saved on the computer system.
Files that have been normally operating cannot be accessed properly anymore and end up with the .HYDRA appendix. Coming from the Jigsaw ransomware family, this malware displays a pop-up window that carries the ransom demands. The authors of the message say that they are interested in playing a game that includes deleting a few files the first day, a hundred the second day, and a few thousand the third day if the ransom demands are still not met.
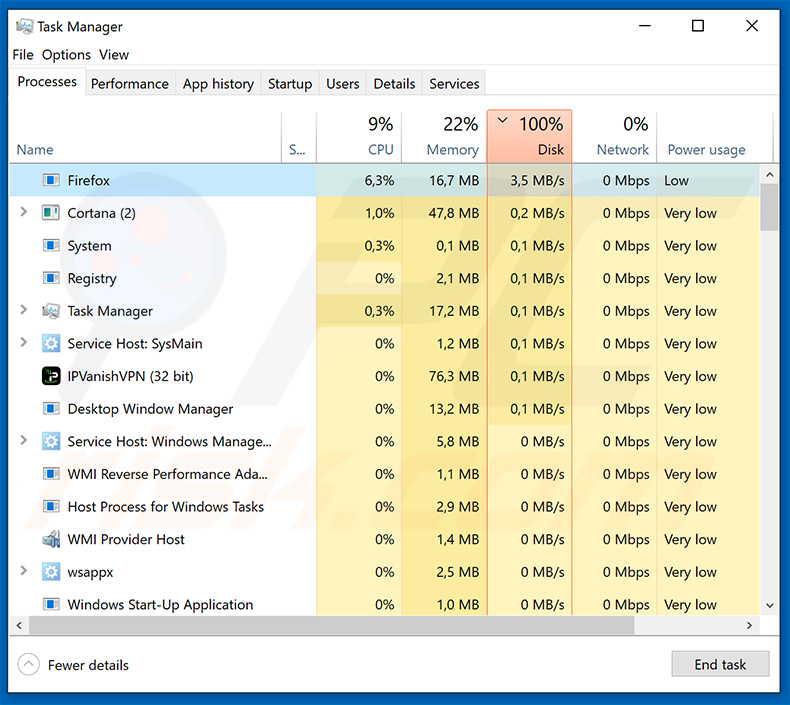
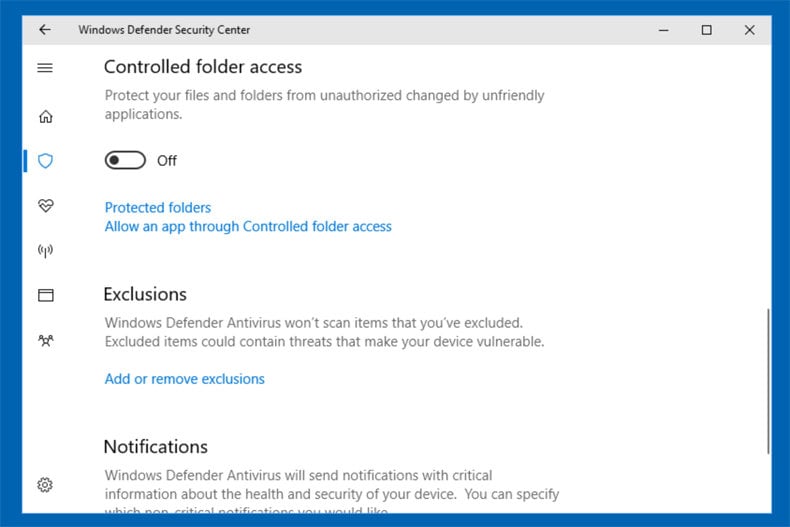
Hydra ransomware attack starts with the modification of entries in the Windows Registry and by adding malicious processes to the Windows Task Manager section. The malware brings an executable to the system that allows to boot up its module every time when the computer is turned on. Some other features might allow the ransomware virus to scan the computer for encryptable files once in a while or even disable antivirus protection to avoid getting detected.
One of the most interest facts regarding Hydra ransomware is that it ends up on the computer as Mozilla Firefox, so you can mix it with your web browser and not know anything suspicious at first. However, when files are encrypted and the .HYDRA appendix is added, you will notice that something is wrong when you cannot properly load your files. Besides, you will also receive this ransom note in a pop-up window slightly after your data is locked with the cipher:
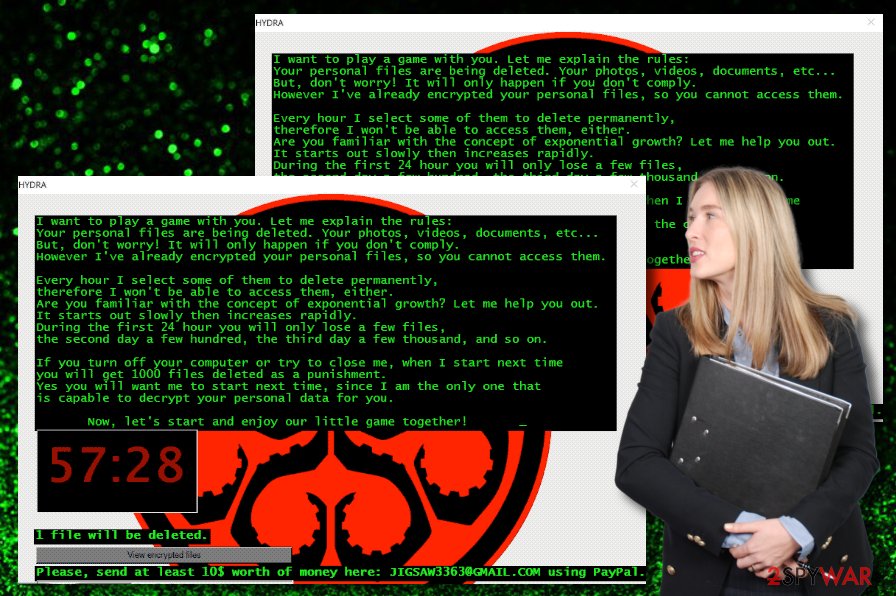
I want to play a game with you. Let me explain the rules:
Your personal files are being deleted. Your photos, videos, documents, etc…
But, don't worry! It will only happen if you don't comply.
However I've already encrypted your personal files, so you cannot access them.
Every hour I select some of them to delete permanently,
therefore I won't be able to access them, either.
Are you familiar with the concept of exponential growth? Let me help you out.
It starts out slowly then increases rapidly.
During the first 24 hour you will only lose a few files,
the second day a few hundred, the third day a few thousand, and so on.
If you turn off your computer or try to close me, when I start next time
you will get 1000 files deleted as a punishment.
Yes you will want me to start next time, since I am the only one that
is capable to decrypt your personal data for you.
Now, let's start and enjoy our little game together!
Bitcoin address: 1Hd3tU8MDmuVotMgGJTJ7svzvPey6bfUgm
Please, send at least 10$ worth of money here: JIGSAW3363@GMAIL.COM using PayPal.
Most of the time malicious actors urge for some type of digital currency payment such as Bitcoin, Ethereum, or Monero. However, Hydra ransomware developers do not seem to bother and go straight for a simple PayPal transfer. However, by asking for $10 as the ransom demand, these people risk exposing themselves for such as small price when cryptocurrency transfers ensure the anonymity of both sides and the criminals stay untrackable.
You should not agree to play the game with these criminals and not get scared because of their promised punishment to eliminate 1000 files if you turn off the computer. Also, you should avoid paying the demanded ransom price even though it is not a big amount. If you transfer the money, you will let the crooks win. Better show these people that you are not scared of them, you can defeat Hydra ransomware and you will search for alternative data recovery solutions.
Hydra ransomware is a family member of Jigsaw ransomware virus
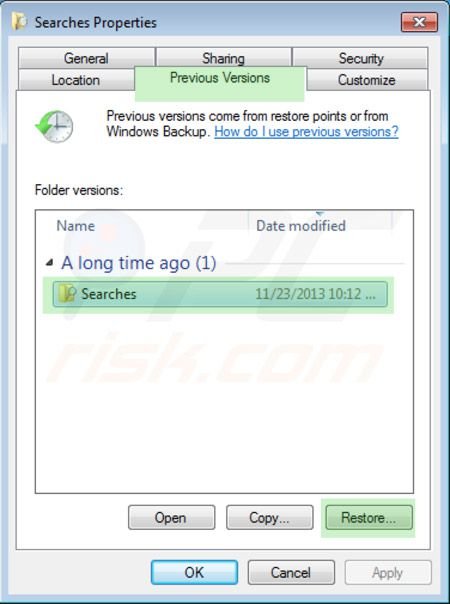
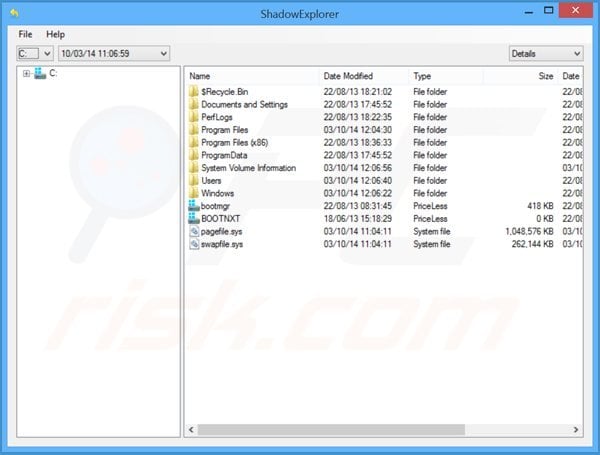
Hydra ransomware might try to harden the file restoring process for you by eliminating the Shadow Volume Copies that are sometimes necessary for third-party data recovery software. Furthermore, the malicious infection might be programmed to damage the Windows hosts files to prevent you from accessing security-related websites. Do not forget to delete these files while dealing with the ransomware, otherwise, the access will still remain blocked.
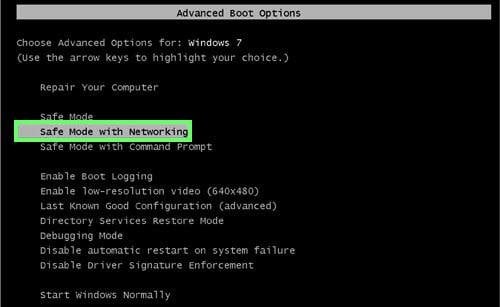
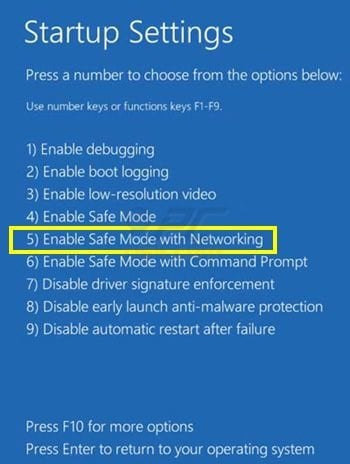
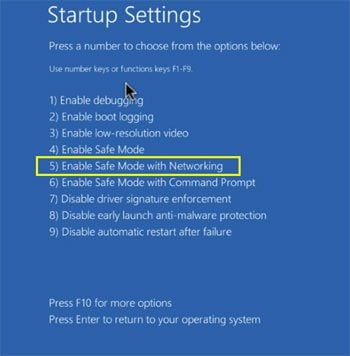
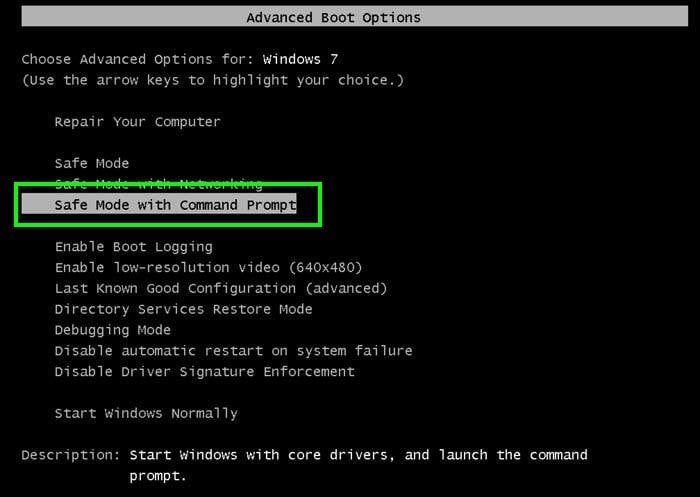
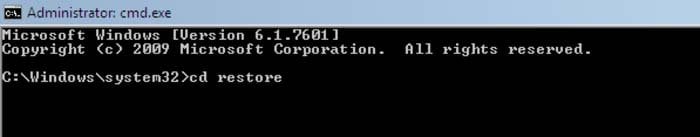
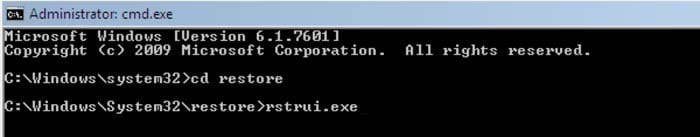
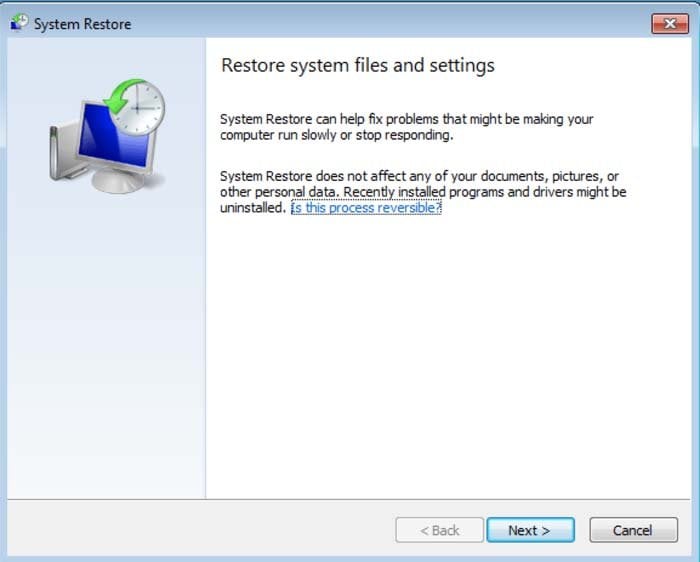
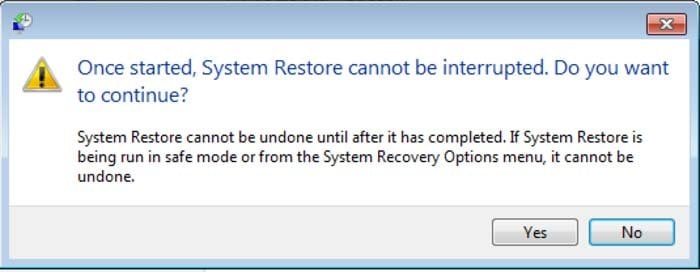
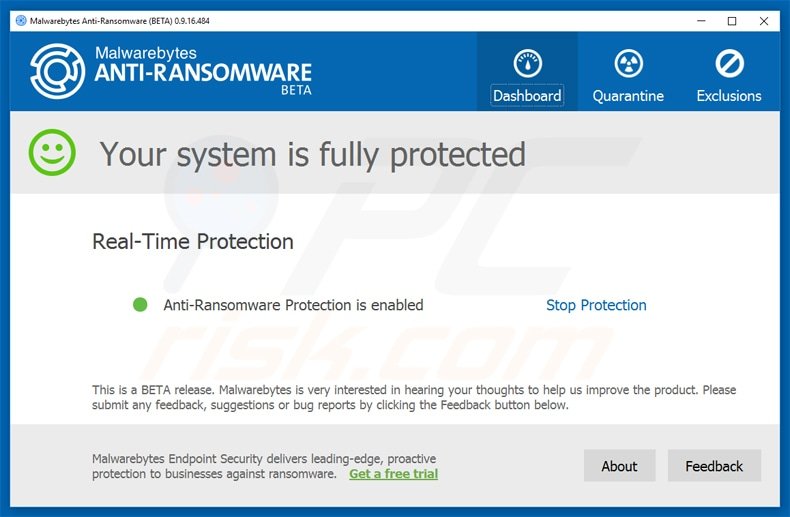
When you see the first signs of infection that include encrypted files and the ransom note, you should hurry up and complete Hydra ransomware removal as this malware might also be programmed to bring other virtual parasites such as trojans to the Windows computer system. If the file-encrypting threat has been blocking your antivirus, you can try diminishing these malicious changes with the help of Safe Mode with Networking.
You should rely on trustworthy and expert-tested antimalware tools that will properly remove Hydra ransomware for you. If you try to complete the elimination by yourself and leave any malicious content lurking on your computer system, the ransomware might return within the next time you start your computer. Also, if you have discovered any damage related to this cyber threat, you can try repairing the corrupted areas by employing software such as Reimage Reimage Cleaner Intego .
Email spam and software cracks are the best malware distributors
Criminals who develop malware such as ransomware [2] want to make sure that the infection reaches its target. For this purpose, they think of various distribution methods that might succeed. Cybersecurity specialists from NoVirus.uk [3] have discovered that ransomware viruses are often spread via email spam.
The malicious payload comes included as an attachment to the message and reaches random people some of whom fall for believing in the received email as hackers pretend to be from reliable-looking companies such as FedEx or DHL and deliver some types of “important notices” that need to be opened immediately.
If you have received an email that you are not sure about, do not hurry to believe in it. First, check if the message is coming from an official address, then, check the entire content for possible grammar mistakes. Lastly, if you have already opted for the downloading process of the attachment, do not open the file without scanning it with reputable antimalware.
Furthermore, malicious payload is also distributed through torrenting networks such as eMule, BitTorrent, and The Pirate Bay. Crooks place the infectious content instead of a game crack, [4] key generator, or as a fake setup and wait for some people to download it. Regarding this fact, get your software from well-known developers only.
The entire elimination process of Hydra ransomware and its malicious payload
Hydra ransomware might have scattered malicious content all over the Windows computer system that needs to be eliminated if you want to get rid of the malware properly. This includes cleaning infecting directories such as the Windows Task Manager, Registry, Control Panel, Desktop, and others.
Also, do not think about performing Hydra ransomware removal with the help of manual technique as this is not a possibility for such a case. The malware is a complex threat to deal with and you have to make sure that it is taken care of properly. Regarding this fact, you should employ only reliable antimalware software.
If you are having a hard time to remove Hydra ransomware from your device, boot it in Safe Mode with Networking and then try again. When the malware is completely gone, you should try searching for damaged areas with the help of SpyHunter 5 Combo Cleaner and Malwarebytes. If this software finds anything corrupted, try fixing the altered products with Reimage Reimage Cleaner Intego .

Written by Tomas Meskauskas on 13 August 2019 (updated)
HYDRA ransomware removal instructions
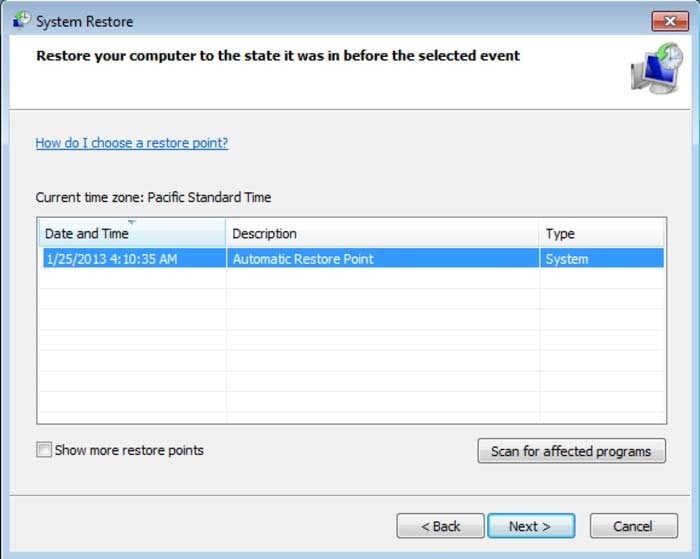
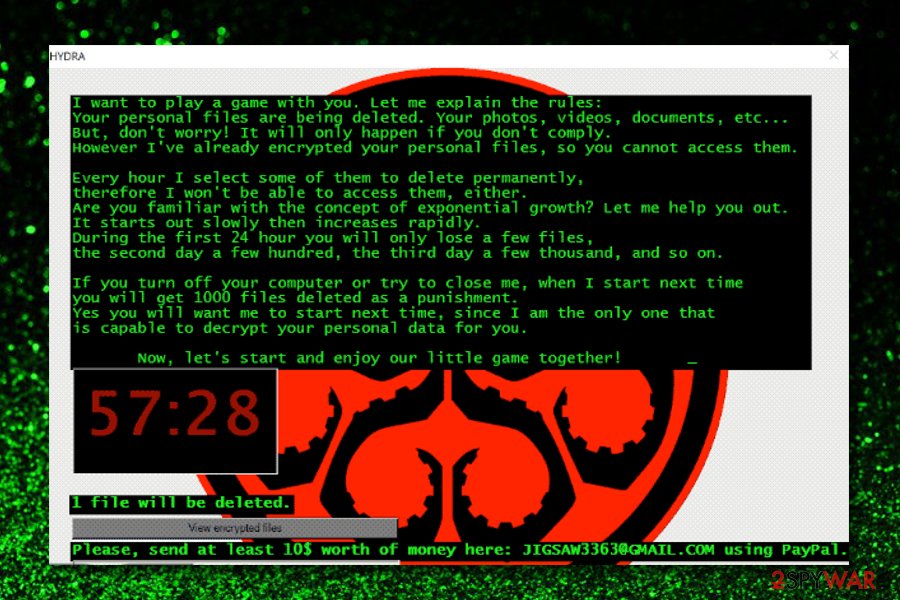
Belonging to the Jigsaw ransomware family, HYDRA is a high-risk ransomware infection discovered by Michael Gillespie. After successfully infiltrating the system, HYDRA encrypts most stored files, rendering them unusable. In addition, HYDRA adds the ".HYDRA" extension to each filename (e.g., "sample.jpg" becomes "sample.jpg.HYDRA"). Once files are completely compromised, HYDRA opens a pop-up window with a ransom-demand message.
The delivered ransom-demand message states that data is being deleted and that victims must pay a ransom to stop the deletion process and restore encrypted files. It goes on to state that the number of deleted files will increase each day (on the first day, a few files; the second day, few hundred; the third day, a few thousand, and so on). Encrypting and deleting files is common behavior for ransomware infections from the Jigsaw family. In this case, the size of ransom is $10, which is rather low (original Jigsaw ransomware demanded $150). Ransoms can be paid using the Bitcoin cryptocurrency and also PayPal. There is a high probability that a third party gained access to Jigsaw ransomware's source code and started to distribute this malware. Furthermore, using PayPal as a payment method is an amateur measure, since the owner can be tracked. Regardless of the cost, do not pay. Research shows that cyber criminals typically ignore victims after payments are submitted. Paying usually gives no positive result. Victims will lose their money and support cyber criminals' malicious businesses. Therefore, never agree to pay. Unfortunately, there are no tools capable of cracking HYDRA encryption and restoring data free of charge (at least not at time of writing). Therefore, the only solution is to restore everything from a backup, if one has been created.
Screenshot of a message encouraging users to pay a ransom to decrypt their compromised data:
HYDRA shares many similarities with Budak, Ims00ry, JSWRM, Adame, and hundreds of other ransomware-type infections. Most ransomware encrypts data so that developers can blackmail victims by offering paid recovery of their files. There are usually just two major differences: 1) size of ransom, and; 2) type of cryptography used. Unfortunately, most infections use RSA, AES, and other encryption algorithms that generate unique decryption keys, which criminals store on remote servers. Therefore, restoring data without the involvement of developers is virtually impossible. The only possible scenarios are the ransomware not being fully developed and/or having certain bugs/flaws (e.g., the key is hard-coded, stored locally, or similar). Ransomware infections present a strong case for maintaining regular backups. Bear in mind, however, that locally stored backups are compromised together with regular data. Therefore, backups should be stored on a remote servers or unplugged storage devices. Note that there is always the chance that servers/storage devices can be damaged, so have multiple backup copies stored in different locations.
Ransomware infections such as HYDRA are typically proliferated using fake software updaters and 'cracks', trojans, third party software download sources, and spam email campaigns. Most fake updaters infect computers by exploiting outdated software bugs/flaws or simply download/installing malware rather than the promised/expected updates. Cracks also have similar behavior - they inject malware rather than activating paid software free of charge. Trojans are essentially malicious applications that stealthily infiltrate computers to inject additional malware. Cyber criminals use third party download sources (peer-to-peer [P2P] networks, freeware download websites, free file hosting sites, and similar) to proliferate malware by presenting it as legitimate software. In this way, users end up manually downloading and installing malware. Finally, cyber criminals use spam email campaigns to send hundreds of thousands of emails containing malicious attachments (links/files) and messages encouraging recipients to open them. These attachments might also be presented as 'important documents' (e.g., invoices, bills, receipts, or similar). This in an attempt to give the impression of legitimacy. In summary, the main reasons for computer infections are poor knowledge of these threats and careless behavior.
| Name | HYDRA virus |
| Threat Type | Ransomware, Crypto Virus, Files locker |
| Encrypted Files Extension | .HYDRA |
| Ransom Demanding Message | Pop-up window. |
| Ransom Amount | $10 |
| Cyber Criminal Contact | jigsaw3363@gmail.com |
| Detection Names | Avast (MSIL:JigSaw-A [Trj]), BitDefender (Generic.MSIL.Ransomware.Jigsaw.607E34D6), ESET-NOD32 (A Variant Of MSIL/Filecoder.Jigsaw.B), Kaspersky (HEUR:Trojan.Win32.Generic), Full List Of Detections (VirusTotal) |
| Rogue Process Name | Firefox (this ransomware is disguised as the Mozilla Firefox web browser) |
| Symptoms | Cannot open files stored on your computer, previously functional files now have a different extension (for example, my.docx.locked). A ransom demand message is displayed on your desktop. Cyber criminals demand payment of a ransom (usually in bitcoins) to unlock your files. |
| Distribution methods | Infected email attachments (macros), torrent websites, malicious ads. |
| Damage | All files are encrypted and cannot be opened without paying a ransom. Additional password-stealing trojans and malware infections can be installed together with a ransomware infection. |
| Malware Removal (Windows) |